Mastering Routing: What is VLSM and How to Design Infallible Topologies
Mastering Routing: What is VLSM and How to Design Infallible Topologies
Welcome back to CodeWithBotina. When we start diving into the world of infrastructure, there comes a time when we must put the code aside for a moment and face IP addressing.
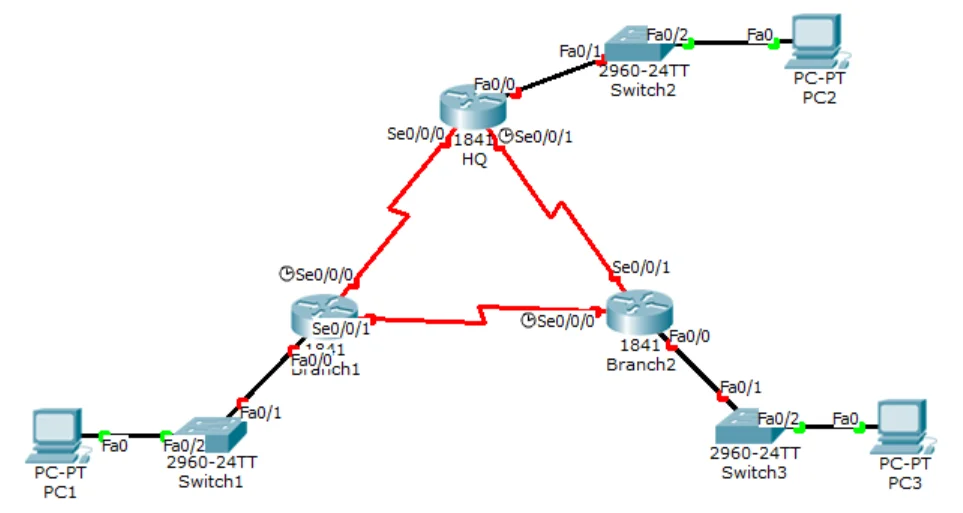
If you have ever sat down to configure a complex topology with multiple routers and switches, you know that a poorly calculated addressing table is the beginning of the end. Today we are going to talk about the ultimate method to ensure you never run out of (nor waste) IP addresses: VLSM (Variable Length Subnet Mask).
1. What is VLSM and why do we need it?
Imagine you have a large pizza and you have to share it. The traditional networking method (FLSM - Fixed Length Subnet Mask) forces you to cut the pizza into exactly equal slices. If the "Sales" department needs 50 IP addresses and the serial link between two routers only needs 2 addresses, with FLSM you would end up assigning 50 IPs to that serial link, catastrophically wasting 48 addresses.
VLSM (Variable Length Subnet Mask) is the solution. It allows you to divide a network into subnets of different sizes. You give a large slice to "Sales", a medium slice to "Support", and a tiny slice (of only 2 usable IPs) to the point-to-point connections between your routers.
It is the absolute standard for designing efficient infrastructures.
2. The Infallible Method: How to calculate VLSM step by step
Calculating VLSM might seem intimidating, but if you follow this golden rule, your addressing table will be bulletproof: Always calculate from the largest subnet to the smallest.
Let's say we are given the main network 192.168.1.0/24 and we need three subnets:
- Network A: 60 hosts
- Network B: 25 hosts
- Network C (Router to Router link): 2 hosts
Step 1: Sort from largest to smallest
Never break this rule. We sort our requirements: 60, 25, and 2.
Step 2: Find the magic number (2^n - 2)
For each network, we need to find how many host bits (n) we need to use so that the formula 2^n - 2 is greater than or equal to the number of hosts requested. (We subtract 2 because we lose the network IP and the broadcast IP).
For Network A (60 hosts):
2^6 - 2 = 62 usable hosts. We need 6 host bits.- New mask: 32 - 6 = /26
- Range: 192.168.1.0 to 192.168.1.63
For Network B (25 hosts): We start from the next available IP (192.168.1.64).
2^5 - 2 = 30 usable hosts. We need 5 host bits.- New mask: 32 - 5 = /27
- Range: 192.168.1.64 to 192.168.1.95
For Network C (2 hosts): We start from 192.168.1.96.
2^2 - 2 = 2 usable hosts. We need 2 host bits.- New mask: 32 - 2 = /30
- Range: 192.168.1.96 to 192.168.1.99
3. Why is it the king of infrastructure topology?
Implementing VLSM is not just a mathematical whim; it is an engineering necessity.
- Massive address saving: Especially in IPv4, where addresses are exhausted.
- Optimized routing tables: Allows routers to group addresses (route summarization), making the network faster and reducing the router's RAM consumption.
- Scalability: If you design your blocks well with VLSM, you can leave calculated "gaps" in your addressing table for when the university or the company needs to add a new department without having to reconfigure the entire network.
Mastering VLSM is what separates an amateur from someone who can truly build a stable infrastructure. Grab a pencil and paper, and start calculating!
Configure, connect, and route without fear. Keep learning at CodeWithBotina.
Loading reactions...
Comments (0)
Loading session...
No comments yet. Be the first to comment.